Check Listening Ports in Linux (Ports in use)


What is a Cyber Attack?
A digital assault is deliberate double-dealing of PC frameworks, organizations, and innovation subordinate ventures. These assaults utilize malevolent code to alter PC code, information, or rationale. Coming full circle into disastrous outcomes that can think twice about information and proclaim cybercrimes like data and fraud. A digital assault is otherwise called a PC network assault (CNA)
Phishing is a sort of friendly design normally utilized to take client information, for example, Mastercard numbers and login qualifications. It happens when an assailant, acting like a confided-in individual, deceives the casualty to open an instant message, email, or text. The casualty is then deluded to open a vindictive connection that can cause the freezing of a framework as a feature of a ransomware assault, uncovering touchy data, or establishment of malware.
Phishing is frequently used to get traction in legislative or corporate organizations as a component of a more huge plot like a high level of diligent danger (APT). In such a case, representatives are compromised to acquire restricted admittance to get information, disperse malware in a shut climate, and sidestep security boundaries.
Spear phishing is an email focused on a specific individual or association, wanting unapproved admittance to significant data. These hacks are not executed by irregular aggressors yet are doubtlessly finished by people out for proprietary innovations, monetary benefit, or military insight.
Skewer phishing messages seem to begin from a person inside the beneficiary's own association or somebody the objective knows actually. Frequently, government-supported hacktivists and programmers play out these exercises. Cybercriminals likewise do these assaults fully intent on exchanging classified information to privately owned businesses and state-run administrations. These assailants utilize social designing and independently planned ways to deal with really customize sites and messages.
A drive-by assault is a typical technique for circulating malware.
A digital assailant searches for a shaky site and plants pernicious content into PHP or HTTP in one of the pages. This content can introduce malware into the PC that visits this site or become an IFRAME that diverts the casualty's program into a site constrained by the assailant. By and large, these contents are jumbled, and this makes the code to be confounded to investigate by security scientists. These assaults are known as a drive-by on the grounds that they don't need any activity on the casualty's part aside from visiting the compromised site. At the point when they visit the compromised site, they naturally and quietly become tainted assuming that their PC is powerless against the malware, particularly in the event that they have not applied security updates to their applications.
A Trojan is a malicious software program that misrepresents itself to appear useful. They spread by looking like routine software and persuading a victim to install it. Trojans are considered among the most dangerous type of all malware, as they are often designed to steal financial information.
SQL injection, also known as SQLI, is a kind of attack that employs malicious code to manipulate backend databases to access information that was not intended for display. This may include numerous items including private customer details, user lists, or sensitive company data.
SQLI can have devastating effects on a business. A successful SQLI attack can cause deletion of entire tables, unauthorized viewing of user lists, and in some cases, the attacker can gain administrative access to a database. These can be highly detrimental to a business. When calculating the probable cost of SQLI, you need to consider the loss of customer trust in case personal information like addresses, credit card details, and phone numbers are stolen.
Cross-webpage prearranging (XSS) is a sort of infusion break where the aggressor sends noxious content into content from in any case respectable sites. It happens when a questionable source is permitted to connect its own code into web applications, and the malevolent code is packaged along with a dynamic substance that is then shipped off the casualty's program.
Malignant code is typically sent as bits of Javascript code executed by the objective's program. The adventures can remember malignant executable contents for some dialects including Flash, HTML, Java, and Ajax. XSS assaults can be extremely crushing, notwithstanding, reducing the weaknesses that empower these assaults is generally basic.
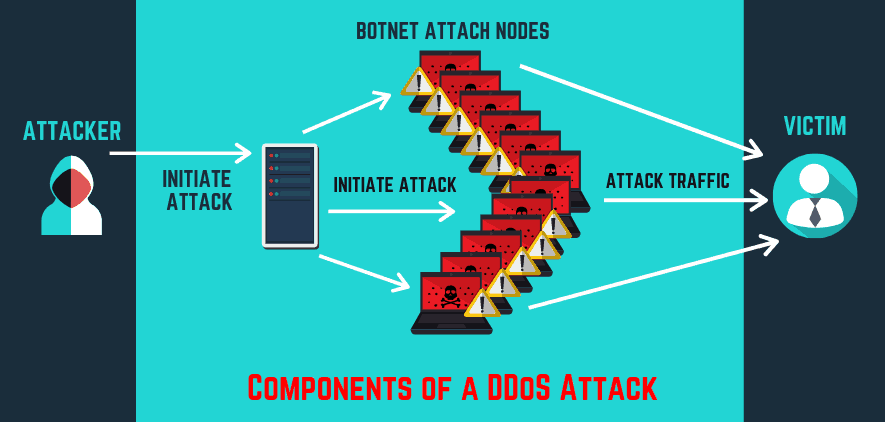
Forswearing of administration (DDoS) targets closing down an organization or administration, making it be blocked off to its planned clients. The assaults achieve this mission by overpowering the objective with traffic or flooding it with data that sets off an accident. In the two circumstances, the DoS attack denies genuine clients like workers, account holders, and individuals from the asset or administration they anticipated.
DDoS assaults are regularly focused on web servers of high-profile associations, for example, exchange associations and government, media organizations, trade, and banking. Albeit these assaults don't bring about the misfortune or burglary of indispensable data or different resources, they can cost casualty loads of cash and time to relieve. DDoS is frequently utilized in a mix to divert from other organization assaults.
Comments
Post a Comment