Check Listening Ports in Linux (Ports in use)


Instructions to Prevent DDoS Attacks:
7 Tried-and-Tested Methods
A DDoS assault empowers a programmer to flood an organization or server with counterfeit traffic. An excess of traffic over-burdens assets and upsets availability, preventing the framework from handling certified client demands. Administrations become inaccessible, and the objective organization experiences delayed personal time, lost income, and disappointed clients.
This article clarifies how a business can forestall DDoS assaults and remain a stride in front of would-be programmers. The practices we show underneath assist with limiting the effect of a DDoS and guarantee a speedy recuperation from an assault endeavor
What Is a DDoS Attack?
A DDoS (Distributed Denial of Service) is a cyberattack that intends to crash an organization, administration, or server by flooding the framework with counterfeit traffic. The abrupt spike in messages, association solicitations, or parcels overpowers the objective's foundation and makes the framework delayed down or crash.
While certain programmers use DDoS assaults to extort a business into paying a payment (like ransomware), more normal thought processes behind a DDoS are to:
Upset administrations or interchanges.
Incur brand harm.
Acquire a business advantage while a contender's site is down.
Occupy the episode reaction group.
DDoS assaults are a threat to organizations, everything being equal, from Fortune 500 organizations to little e-retailers. Measurably, DDoS programmers most frequently target:
Online retailers.
IT specialist co-ops.
Monetary and fintech organizations.
Government substances.
Web based gaming and betting organizations.
Assailants ordinarily utilize a botnet to cause a DDoS. A botnet is a connected organization of malware-contaminated PCs, cell phones, and IoT contraptions under the assailant's influence. Programmers utilize these "zombie" gadgets to send unnecessary quantities of solicitations to an objective site or server's IP address.
Once the botnet sends an adequate number of solicitations, online administrations (messages, sites, web applications, and so forth) dial back or come up short. As per a Radware report, these are the normal lengths of a DDoS assault:
33% keep administrations inaccessible for 60 minutes.
60% last under an entire day.
15% keep going for a month.
While a DDoS normally doesn't straightforwardly prompt an information break or spillage, the casualty invests energy and cash getting administrations back on the web. Loss of business, deserted shopping baskets, disappointed clients, and reputational hurt are common outcomes of neglecting to forestall DDoS assaults.
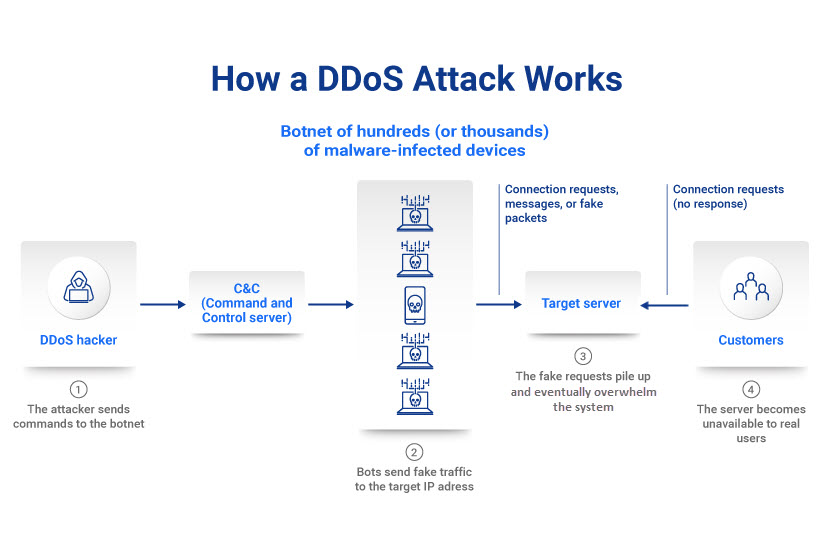 ................How a DDoS assault functions.............
................How a DDoS assault functions.............
Types of DDoS Attacks
While all DDoS attacks aim to overwhelm a system with too much activity, hackers have different strategies they rely on to cause a distributed denial of service.
The three main types of attack are:
Application-layer attacks.
Protocol attacks.
Volumetric attacks.
The three approaches rely on different techniques, but a skilled hacker can employ all three strategies to overwhelm a single target.
Application-Layer Attacks
An application-layer assault targets and upsets a particular application, not a whole organization. A programmer creates countless HTTP demands that exhaust the objective server's capacity to answer.
Network safety experts measure application layer assaults in demands each second (RPS). Normal focuses of these assaults include:
Web applications.
Web associated applications.
Cloud administrations.
Attempting to forestall DDoS assaults of this kind is trying as security groups frequently battle to recognize genuine and malevolent HTTP demands. These assaults utilize less assets than other DDoS techniques, and a few programmers might actually utilize just a solitary gadget to organize an application-layer assault.
One more typical name for an application level DDoS is a layer 7 assault.
Protocol Attacks
Convention DDoS assaults (or organization layer assaults) exploit shortcomings in the conventions or techniques that administer web interchanges. While an application level DDoS focuses on a particular application, the objective of a convention assault is to dial back the whole organization.
The two most normal kinds of convention based DDoS assaults are:
SYN floods: This assault takes advantage of the TCP handshake methodology. An assailant sends TCP demands with counterfeit IP locations to the objective. The objective framework answers and trusts that the shipper will affirm the handshake. As the aggressor never sends the reaction to finish the handshake, the inadequate cycles stack up and ultimately crash the server.
Smurf DDoS: A programmer utilizes malware to make an organization bundle joined to a misleading IP address (mocking). The bundle contains an ICMP ping message that requests that the organization send back an answer. The programmer sends the reactions (reverberations) back to the organization IP address once more, making an endless circle that ultimately crashes the framework.
Network protection specialists measure convention assaults in parcels each second (PPS) or bits each second (BPS). The principle motivation behind why convention DDoS is so boundless is that these assaults can undoubtedly sidestep ineffectively arranged firewalls.
Volumetric Attacks
A volume-based DDoS assault consumes an objective's accessible transfer speed with bogus information demands and makes network clog. The assailant's traffic blocks authentic clients from getting to administrations, keeping traffic from streaming in or out.
The most widely recognized kinds of volumetric DDoS assault types are:
UDP floods: These assaults permit a programmer to overpower ports on the objective host with IP parcels containing the stateless UDP convention.
DNS enhancement (or DNS reflection): This assault diverts high measures of DNS solicitations to the objective's IP address.
ICMP flood: This technique utilizes ICMP misleading mistake solicitations to over-burden the organization's data transfer capacity.
All volumetric assaults depend on botnets. Programmers use multitudes of malware-contaminated gadgets to cause traffic spikes and go through all suitable data transmission. Volumetric assaults are the most widely recognized sort of DDoS.
7 Best Practices to Prevent DDoS Attacks
While it is absolutely impossible to keep a programmer from endeavoring to cause a DDoS, appropriate preparation and proactive measures decrease the gamble and expected effect of an assault.
Make a DDoS Response Plan
Your security group ought to foster an occurrence reaction plan that guarantees staff individuals answer instantly and really in the event of a DDoS. This arrangement should cover:
Clear, bit-by-bit directions on the most proficient method to respond to a DDoS assault.
Comments
Post a Comment